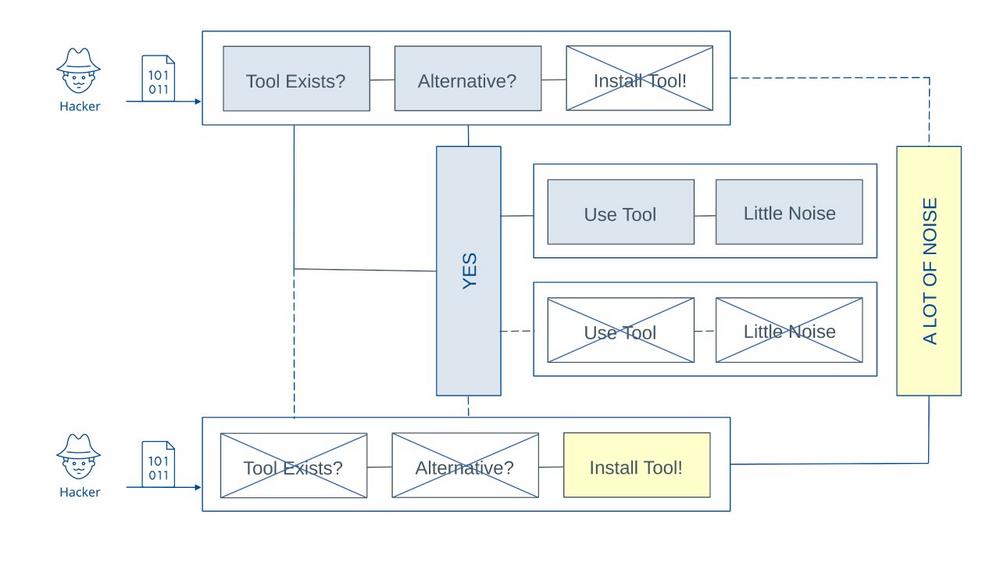
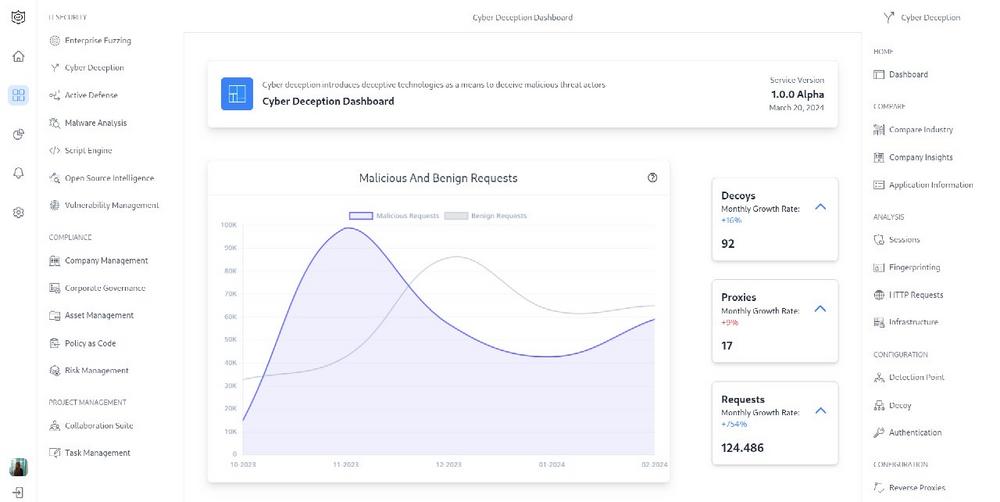
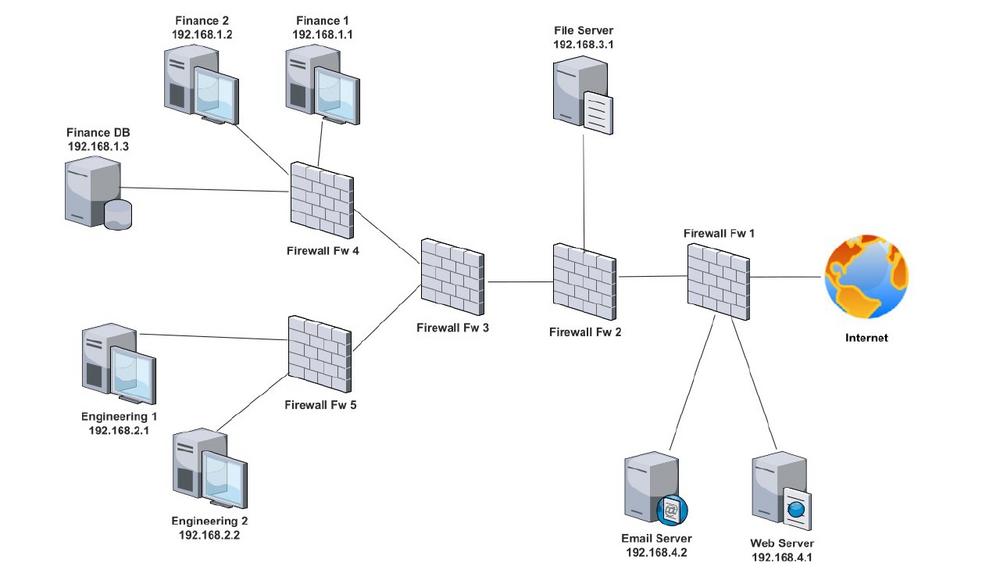
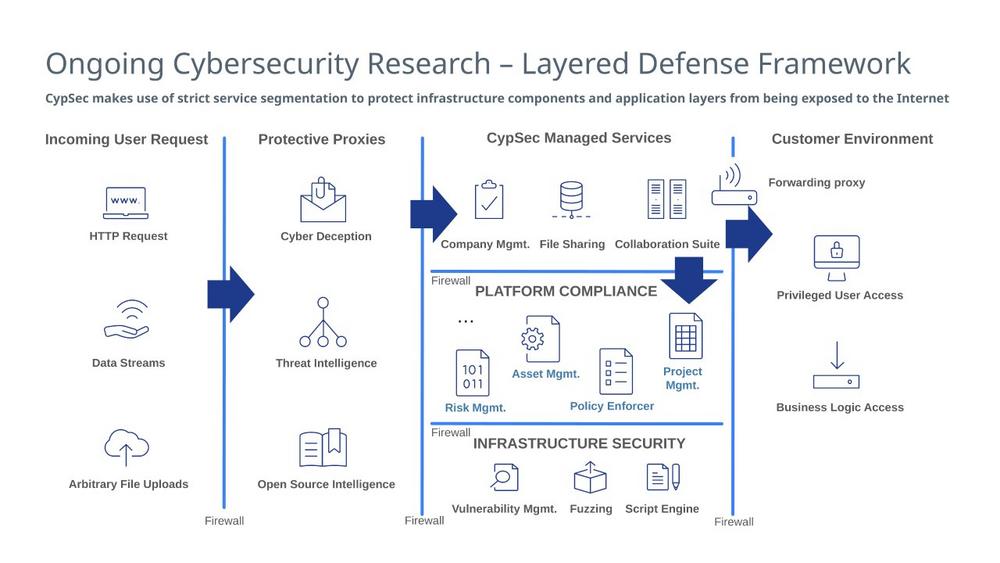
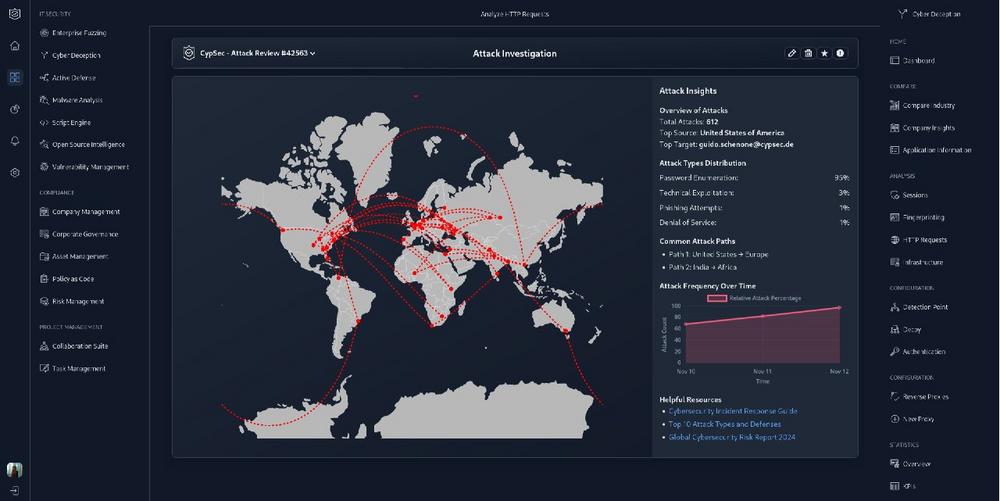
CypSec-research introducing the "Follow the Noise" methodology for detecting sophisticated cyber intrusions through behavioral analysis of attacker tool usage in honeypot environments. The research demonstrates that advanced adversaries, despite their sophistication, generate distinctive detectable patterns through their post-compromise activities. These patterns emerge from the tension between using available tools, installing custom utilities, or pursuing alternative […]
continue reading